How HITRUST Provides Superior PHI Protection
Due to its highly personal nature, patient healthcare information, often including Social Security numbers, birth dates, addresses, diagnosis codes, and billing details, is among the most valuable and coveted assets on the black market. This trove of information attracts cybercriminals for reasons beyond mere identity theft. Unfortunately, protection of such data still lags across the healthcare industry.
Motivated by potential financial gain, malicious actors engage in a variety of illegal activities, including reselling stolen drugs and medical equipment, filing fraudulent insurance claims worth millions, and exploiting credentials to access high value systems. Stolen healthcare records consistently command a premium compared to credit cards or other financial data.
Healthcare organizations often lag in implementing robust cybersecurity measures, making them prime targets for cyberattacks. This vulnerability is reflected in alarming and rising trends of breaches and data exposure across the healthcare industry.
Alarming statistics regarding cybersecurity in the healthcare industry and the lack of PHI protection
- In 2024, the U.S. Office for Civil Rights recorded 725 large healthcare breaches affecting 500 or more records. This was the third consecutive year with more than 700 major breaches.
- That same year, the number of exposed records surged to approximately 276 million, which represents about 81 percent of the U.S. population.
- The average cost of a healthcare data breach in the United States in 2025 is now 7.42 million dollars per incident, the highest across all industries.
- On a per-record basis, the average cost in healthcare is now approximately 398 dollars for every exposed record.
- The healthcare industry accounted for 23 percent of all data breaches handled by risk advisory firm Kroll in 2024, making it the most frequently breached industry that year.
- On the black market, full medical records continue to be far more valuable than credit cards. Some estimates place the cost of a complete medical profile between 250 and 1,000 dollars on certain dark web marketplaces.
These trends show that it is increasingly important for healthcare organizations to implement the strongest possible safeguards to protect sensitive patient information.
HIPAA’s shortcomings that led to increased risk
The Health Insurance Portability and Accountability Act was enacted more than twenty years ago to protect sensitive medical information, including electronic data. HIPAA outlines security safeguards across administrative, physical, and technical domains and applies to all healthcare organizations and providers.
However, HIPAA allows organizations to perform their own risk assessments and determine the level of security controls appropriate for their environment. Many organizations have struggled with this responsibility. Without clear guidance on how to implement required safeguards while remaining compliant, many organizations failed to put strong controls in place. As a result, patient data often remained vulnerable.
Ransomware and emerging attack trends in healthcare
As healthcare organizations continue to rely on digital systems, ransomware and other sophisticated attacks have become some of the most significant threats facing the industry.
- During the first half of 2025, the healthcare sector experienced 211 ransomware incidents worldwide.
- These confirmed attacks exposed at least 2.37 million patient records during that period.
- The average ransom demand for healthcare organizations in early 2025 was approximately 479,000 dollars.
- One major attack in 2025 affected an estimated 190 million individuals, underscoring the scale of modern threats.
- The median time to identify and contain a healthcare breach in 2025 is approximately 241 days.
Ransomware affects far more than data confidentiality. It disrupts clinical workflows, scheduling, billing, and patient safety. Because medical data cannot simply be replaced or reset, the risk to patients is long-term and significant.
Recommended actions
- Maintain offline and regularly tested backups.
- Segment networks to limit lateral movement by attackers.
- Conduct tabletop exercises that simulate real ransomware scenarios.
- Include ransomware-specific requirements in vendor contracts.
- Monitor emerging threats, including attacks against medical device firmware and third-party systems.
Vendor and third-party risk, and the rise of supply chain exposure
Modern attacks often enter through trusted vendors, business associates, cloud platforms, and software supply chains. A secure healthcare organization is still vulnerable if one of its partners is compromised.
- In the first five months of 2025, 311 data breaches involving 500 or more individuals were reported, affecting approximately 23.1 million people.
- Vendor-side breaches are especially damaging. In 2023, business associates or vendors were responsible for nearly two-thirds of all compromised records in major healthcare breaches.
- Threat actors continue to exploit client-side vulnerabilities such as third-party scripts running on patient portals and other web applications.
- Third-party breach reports show rapid growth in vendor-related incidents, making extended ecosystem risk one of the fastest-increasing concerns in healthcare security.
Recommended actions
- Maintain a vendor risk register that tracks service providers handling PHI, including their certifications, controls, and incident history.
- Require rapid notification from vendors in the event of a security incident.
- Implement least privilege access rules for all vendor personnel.
- Conduct due diligence assessments of vendor security controls.
- Use contractual agreements that clearly outline responsibilities and expectations for security and breach response.
- Monitor client-side risk by assessing all third-party scripts and components used in patient-facing applications.
Development of the HITRUST Alliance and the CSF framework
In 2007, industry leaders recognized the need for a unified and comprehensive information security framework for healthcare. This led to the creation of the HITRUST Alliance and the HITRUST CSF. This nonprofit organization focuses on information risk management, the development of security frameworks, and compliance support. The HITRUST CSF is now one of the most widely adopted security and privacy risk management frameworks in the United States healthcare sector.

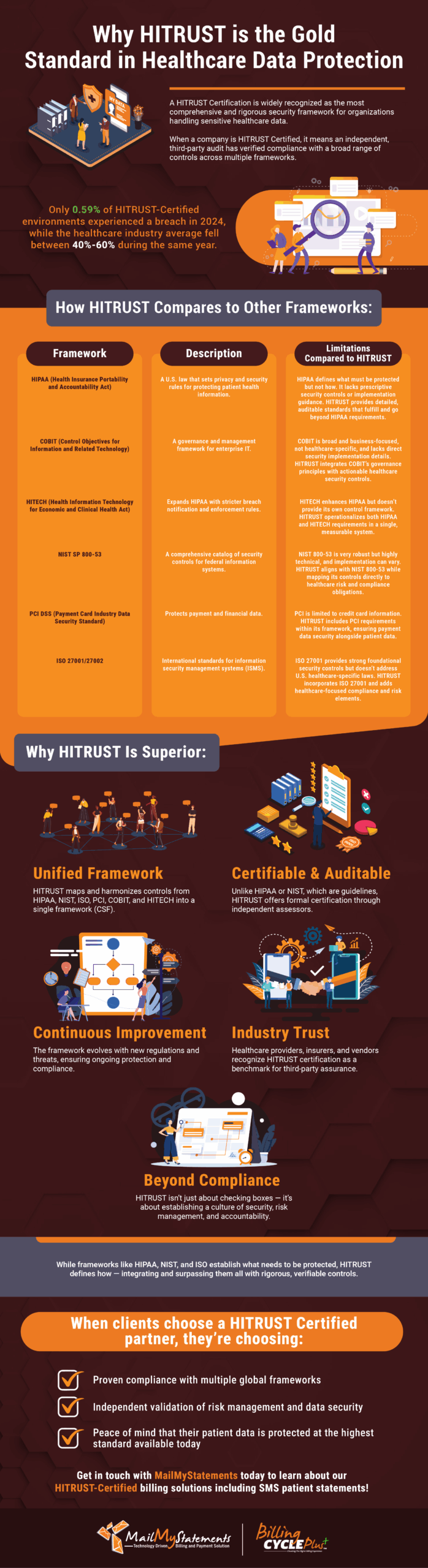
HITRUST certification provides prescriptive controls across a broad range of regulations
HITRUST certification offers vendors and medical billing providers a prescriptive set of guidelines that help them meet security and compliance objectives across multiple regulatory requirements. The HITRUST approach creates a clear roadmap for managing compliance and reducing risk. By incorporating globally recognized standards and scaling requirements to the size of the organization, HITRUST helps companies save time and money while protecting information and maintaining compliance.
“Within the HIPAA Security Rule, certain specifications are required, and others are addressable. An organization can choose not to implement addressable specifications if there is a valid business reason.”
Joe McDermott, HITRUST Technical Lead at Schellman
HITRUST’s high bar for certification means your data is in trusted hands
HITRUST certification demonstrates that a vendor maintains strong security and compliance practices. This gives partner organizations and parent companies confidence in the vendor’s ability to protect sensitive information. Organizations that hold HITRUST certification are better equipped to protect PHI, reduce risk, maintain compliance, and build trust with patients and partners.
MailMyStatements proudly holds HITRUST certification and takes the protection of partner and patient information very seriously. Contact us today to learn how our technology-driven billing and payment systems can benefit your practice.
LEARN MORE ABOUT HOW OUR SOLUTIONS CAN SAVE YOU TIME AND MONEY
![]()